IT Explained
We at Paessler use IT-related terms constantly, and we are very much aware of the “The Imposter Syndrome”
in IT when professionals continue using terminology they might not even understand themselves. But there are also plenty of new terms in the fields of OT and IoT that many people may not be familiar with, or for which there are even contrary definitions.
At Paessler, we write a lot about IT, OT, and IoT topics. That's why you can find a comprehensive overview of relevant terminology here, which we are constantly updating.
You feel there’s something missing? Get in touch with us!
Question about terminology? Find your answer here!
Active Directory
Active Directory (AD) is a directory service created by Microsoft for use in a Windows Server environment.
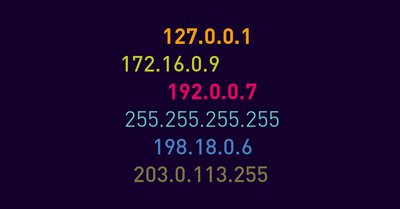
IP address
An IP address is a numerical identifier for a specific interface in the network. ➤ We explain IT concepts - maximise your knowledge now!
Packet Sniffing
Packet sniffing is the practice of gathering, collecting, and logging some or all packets that pass through a computer network.
Retrofitting
Retrofitting is updating or adding equipment, sensors, or services to existing hardware so that it is able to make use of new technologies.
Smart Buildings
Smart buildings deliver actionable information about a building itself or a specific room inside it so that owners or tenants can better manage it.
Smart Cities
A smart city uses information and communication technologies (ICT) to help resolve the traditional challenges of urban living.
Smart Environmental Monitoring
Environmental monitoring involves the capture of any type of data that contributes to showing how the world around us behaves, how it affects our lives, and how it can be controlled.
SSH (Secure Shell)
SSH is an acronym for Secure Shell. It is a generic term that refers to versions of SSH protocols, for example SSH-1 and SSH-2, among other things like OpenSSH.
Unified Communications (UC)
UC stands for unified communications. It describes a framework or standard that incorporates various components such as software, hardware, and services to enhance business communication.
Virtualization
Virtualization is the process of creating a virtual version of something like computer hardware. It allows to create multiple environments from a single system